Earlier this month, I and others wrote a letter to Congress, basically saying that cryptocurrencies are an complete and total disaster, and urging them to regulate the space. Nothing in that letter is out of the ordinary, and is in line with what I wrote about blockchain in 2019. In response, Matthew Green has written—not really a rebuttal—but a “a general response to some of the more common spurious objections…people make to public blockchain systems.” In it, he makes several broad points:
Data Privacy
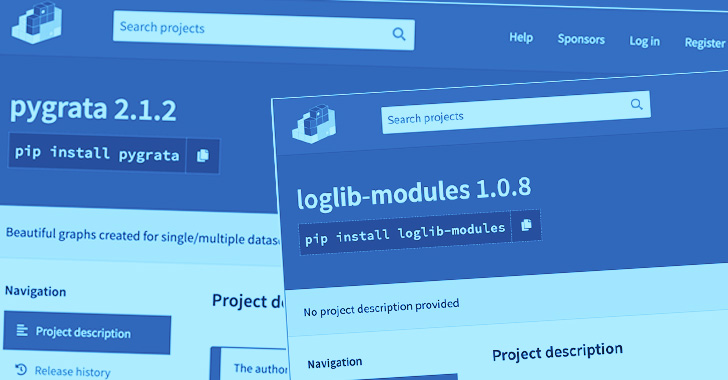
Multiple Backdoored Python Libraries Caught Stealing AWS Secrets and Keys
Researchers have discovered a number of malicious Python packages in the official third-party software repository that are engineered to exfiltrate AWS credentials and environment variables to a publicly exposed endpoint. The list of packages includes loglib-modules, pyg-modules, pygrata, pygrata-utils, and hkg-sol-utils, according to Sonatype security researcher Ax Sharma. The packages and as well as the endpoint have now been taken down. "Some of these packages either contain code that reads and exfiltrates your secrets or use one of the dependencies that will do the job," Sharma said.
What China’s new data privacy law means for US tech firms
Modeled after the EU's GDPR, China's PIPL imposes protections and restrictions on data collection and transfer that companies both inside and outside of China will need to address.
What Does Good Privacy Look Like for Your Organization?
This blog post is not legal advice for your company to use in complying with data privacy laws like GDPR. Instead, it provides background information to help you better understand data privacy best practices. This legal information is not the same as legal advice, where an attorney applies the law to your specific circumstances, so we insist that you consult an attorney if you’d like advice on your interpretation of this information or its accuracy.
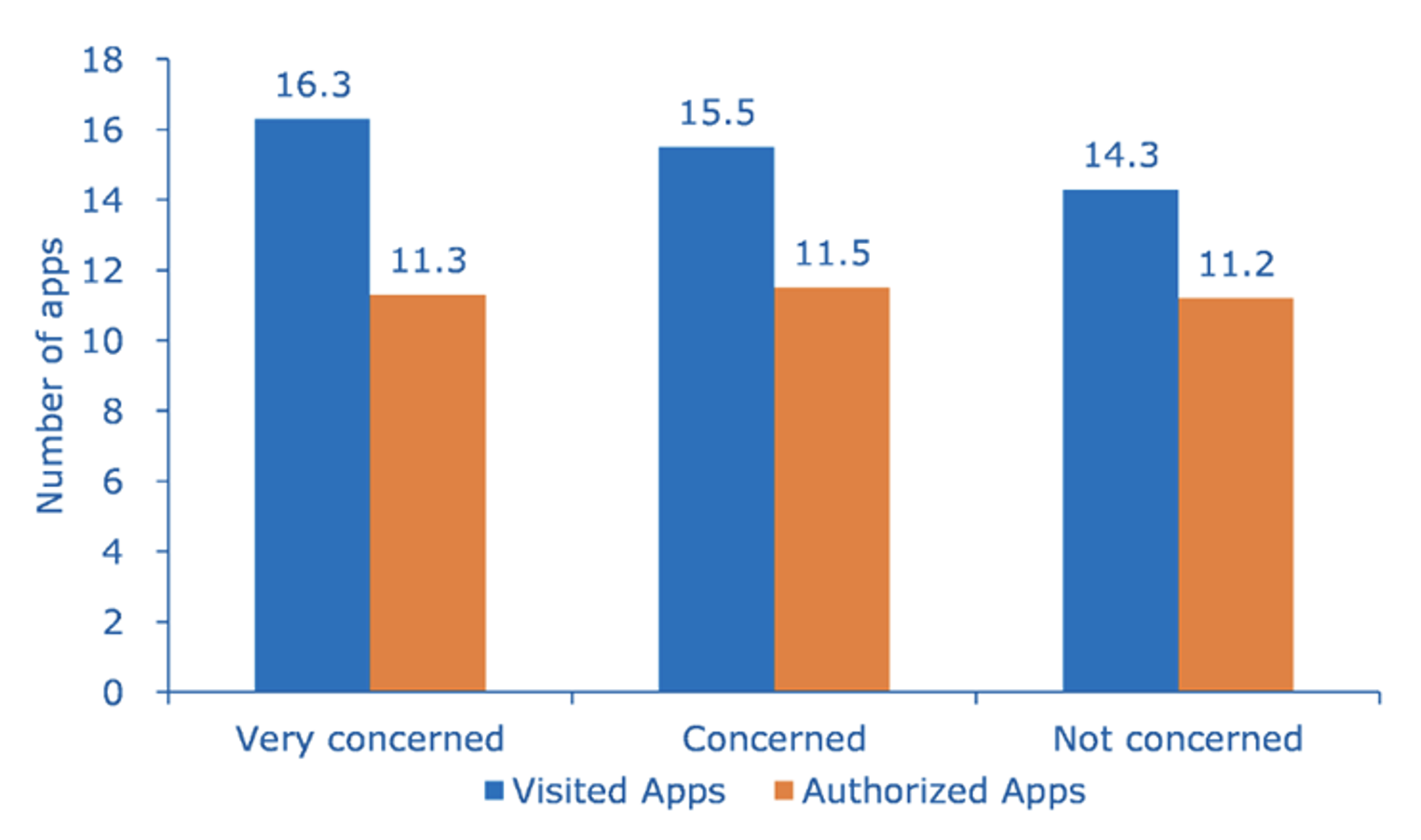
The Data Privacy Paradox and Digital Demand
Data privacy worrywarts appear to be the most promiscuous. What gives?
Banning Surveillance-Based Advertising
The Norwegian Consumer Council just published a fantastic new report: “Time to Ban Surveillance-Based Advertising.” From the Introduction: The challenges caused and entrenched by surveillance-based advertising include, but are not limited to: privacy and data protection infringements opaque business models manipulation and discrimination at scale fraud and other criminal activity serious security risks In the following chapters, we describe various aspects of these challenges and point out how today’s dominant model of online advertising is a threat to consumers, democratic societies, the media, and even to advertisers themselves. These issues are significant and serious enough that we believe that it is time to ban these detrimental practices...
Why you need a secret phone number (and how to get one)
Privacy Please is an ongoing series exploring the ways privacy is violated in the modern world, and what can be done about it. Your phone number was never meant to be an all-access pass to your life. That 10-digit string has likely followed you around the world and across the internet for years. Over the course of that time, you've almost certainly handed it out — willingly or otherwise — to every person, restaurant, social media platform, or online store that's asked. That's a problem. For someone with the right motivation, that number is a thread which, once pulled, can unravel your entire digital life — crashing down your privacy, bank account, or even your very identity.
Your medical records are about to be given away. As GPs, we’re fighting back
GPs in England have been told to hand over all patient data to NHS Digital – potentially to be exploited for corporate profit. GP practices in England have been instructed to hand over their patients’ entire medical histories with just six weeks’ notice. Like many GPs, I’m very concerned about the implications this has for my patients. A growing number of us in London have taken taken the decision to pull the plug on the new data-sharing programme with NHS Digital and refuse to hand over patient records.
How to opt out of (or into) Amazon’s Sidewalk network
Do you own an Echo Studio, an Echo Dot, or a Ring Floodlight Cam? If so, Amazon is about to introduce your device to a new type of network it calls Sidewalk, which is meant to help extend the range of its low-bandwidth devices (so that if your network goes down, for example, your Dot can piggyback on your neighbors’), and also to make location devices such as Tile more efficient.
Trust and Data Analytics: Protecting Privacy in Analysis
Technology gave rise to Data Analytics, but it can also become the cause of several privacy issues. Data Analytics is progressively changing the world. Businesses, governments, and different organizations are unlocking their true potential with the help of Data Analytics. Real-time analytics provides swift solutions to complex problems, enabling faster decision-making, and accelerating investments across all industrial sectors.
The court ruling against GCHQ is just the latest battle in the fight for privacy | Megan Goulding
No matter our background or beliefs, we all want control over our personal information, our private views and our sensitive data. That control is key to our autonomy and our liberty. But in 2013 Edward Snowden pulled back the curtain on how governments had used the excuse of the “war on terror” to erode that liberty.
How Privacy-Enhancing Technologies Can Accelerate Your Data Strategy
As organizations look to safely and securely connect with their partners, executive decision makers are increasingly finding that their strategic discussions on data collaboration need to include privacy-enhancing technologies (PETs). PETs offer businesses the ability to accelerate safe data collaboration, build customer intelligence, and maximize the value of data without relinquishing control or compromising consumer privacy.
Data anonymization layer using Snowflake and DBT
A scalable approach to anonymizing your data on Snowflake using DBTHousingAnywhere is an online marketplace platform for mid to long-term rents. Like any other data-driven business we have to deal with both personal information and GDPR regulations. In this brief article, I’ll walk you through our solution to anonymize PII (Personal Identifiable Information). The technologies that I’ll be using are Snowflake[1], a popular data warehouse cloud solution and DBT[2](Data Build Tool) a data transformation tool.
Divided we fall: Why fragmented global privacy regulation won’t work
The growing patchwork of US state-level privacy laws will inflict significant costs on businesses and the American public.
How User Data Privacy and Antitrust Law Got All Tangled Up
This week, we look at how the latest iPhone software update ties into the debate about regulating big tech.
What are the different roles within cybersecurity?
People talk about the cybersecurity job market like it's a monolith, but there are a number of different roles within cybersecurity, depending not only on your skill level and experience but on what you like to do. In fact, Cybercrime Magazine came up with a list of 50 cybersecurity job titles, while CyberSN, a recruiting organization, came up with its own list of 45 cybersecurity job categories
How startups can ensure CCPA and GDPR compliance in 2021
Small startups might not think the world’s strictest data privacy laws apply to them, but it’s important to enact best data management practices before a legal situation arises.
Who’s Watching Us? Why Privacy Matters. | Aishwarya Rambhatla | TEDxTSIS
After attending the Global summit on Data privacy just a few months ago, Aiswarya found that there was much more to privacy policies than meets the eye. Her speech outlines what corporations truly do with our intellectual property whilst debunking common myths surrounding privacy in general. Year 12 Student at South Island School. This talk was given at a TEDx event using the TED conference format but independently organized by a local community. Learn more at https://www.ted.com/tedxFrom: TEDx Talks
Use the DuckDuckGo Extension to Block FLoC, Google’s New Tracking Method in Chrome
Google has created a new tracking mechanism called FLoC, put it in Chrome, and automatically turned it on for millions of users. It's bad for privacy, which is why we're now blocking it in the DuckDuckGo extension.
Too slow! Booking.com fined for not reporting data breach fast enough
It's not just the breach, it's the speed of the breach response...